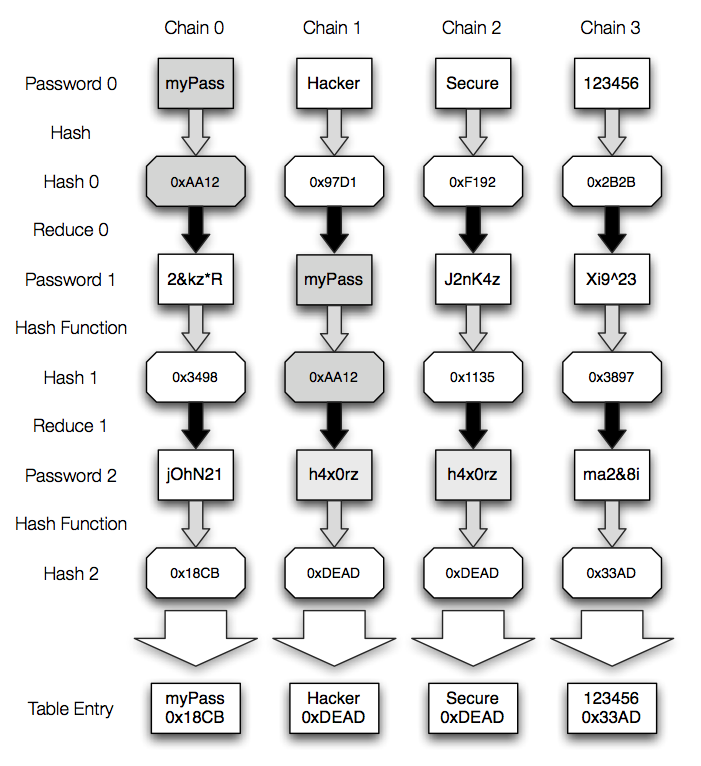
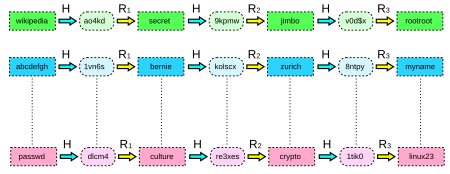
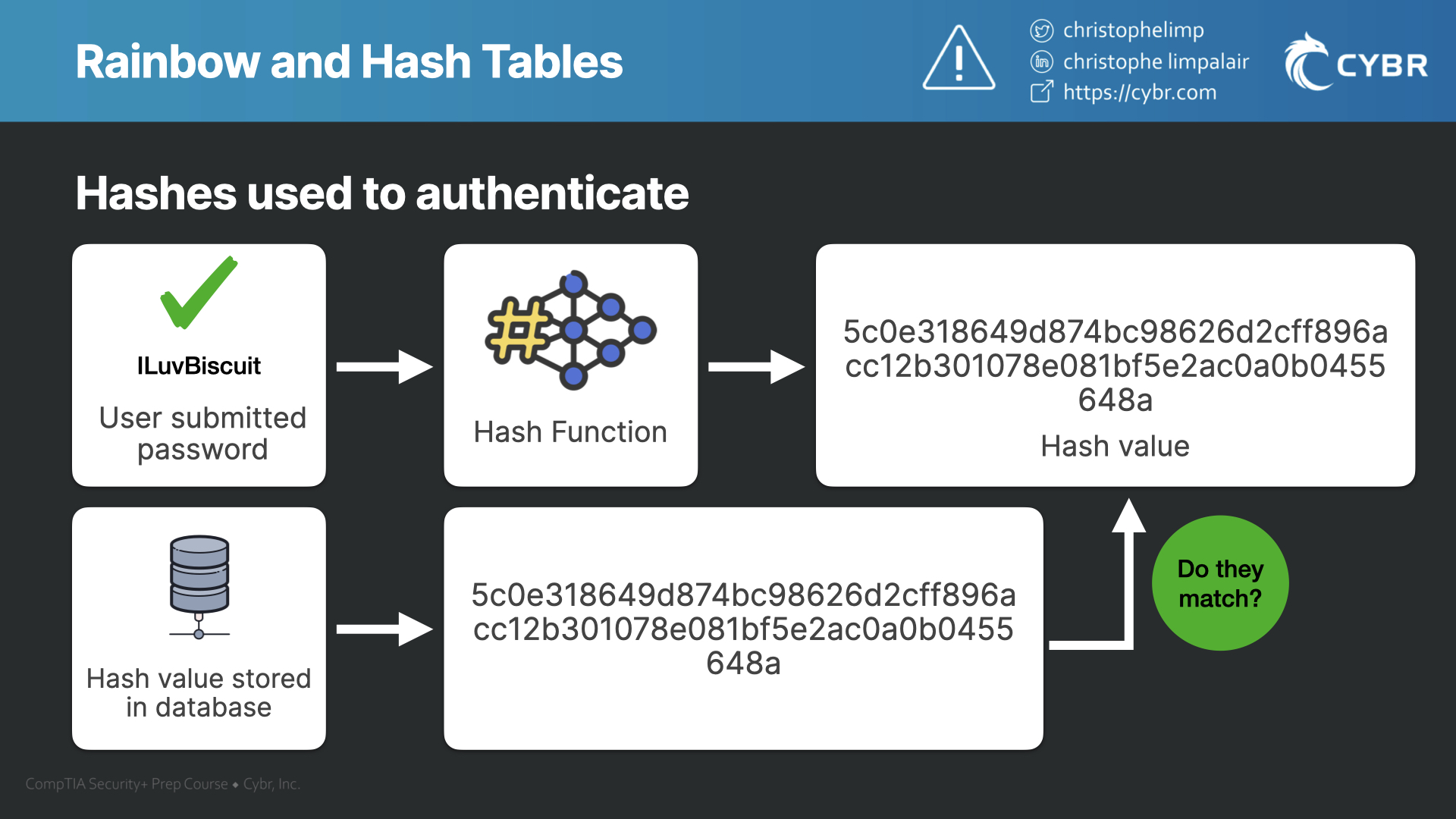
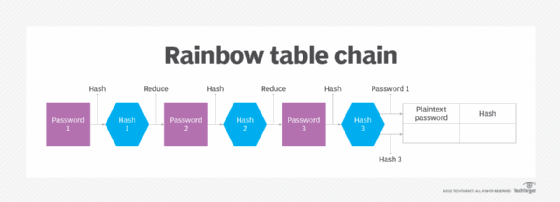
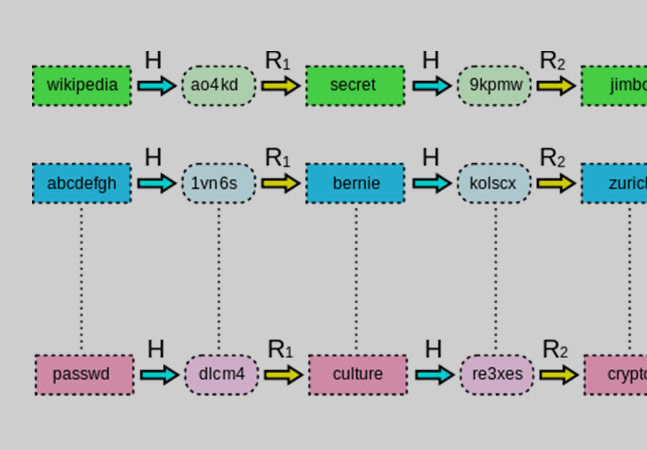
Rainbow Tables (probably) aren't what you think — Part 1: Precomputed Hash Chains | by Ryan Sheasby | Medium

Amazon.com: Nepnuser Rainbow Table Runner Rustic June Pride Month LGBTQ+ Party Decoration Linen Farmhouse Home Dining Room Kitchen Table Decor (13" x 72") : Home & Kitchen